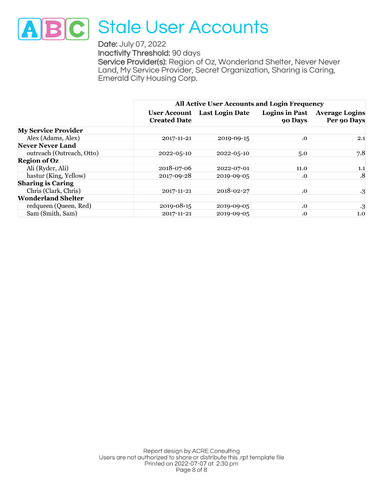
Stale User Accounts
Are your staff actually using the accounts you've set up for them?
- users who haven't agreed to the EULA,
- users who have never logged in,
- users with no logins in a timeframe you specify,
- users with concurrent logins,
- infrequently used accounts,
- if you're using 2FA, user accounts with no security key,
- median days since most recent login, and
- average logins per user.
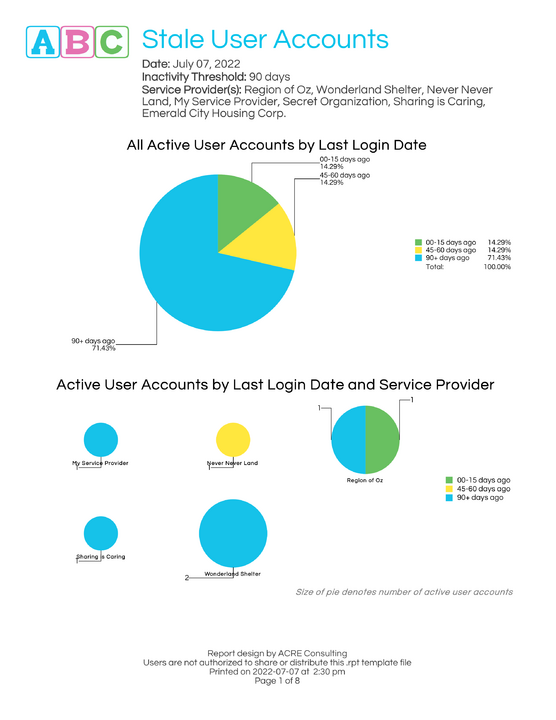
This report identifies stale user accounts, covering: users who haven't agreed to the EULA, users who have never logged in, users with no logins in a timeframe you specify, users with concurrent logins, infrequently used accounts, median days since most recent login, and average logins per user.
What's included?
This 8+ page report aggregates data about user accounts, with the following breakdowns:
- Overall percentages of users by most recent login date, and breakdown by service provider
- Median days since most recent login, by service provider
- Median logins per user in the reporting period
- User accounts with no EULA
- User accounts who have never logged in
- User accounts with no recent logins
- If using 2FA, user accounts with no security key
- User accounts with concurrent logins enabled
- Infrequently used user accounts
What is a stale user account?
Inactive accounts or accounts that have never logged in are also known as “stale” user accounts.
Stale accounts pose a security risk to organizations. Each one of these accounts offers a malicious actor an opportunity to gain access to your data. When stale accounts are unknown or unmonitored, a malicious actor can compromise one and remain hidden to IT staff.
Best practices and standards require that these accounts are removed or disabled within a set amount of time.
Think of it this way; imagine you run a kingdom in medieval times. Each account that is given out or created is a member of your kingdom that has keys to the city. A key (or account) could topple your entire kingdom, as other kingdoms or bandits (malicious actors) want to get into your kingdom to steal anything of value. The more keys (or accounts) you can remove from circulation, the more secure your kingdom is.
Frequently Asked Questions
What version of HIFIS is required to run this report?
This report should run on any version of HIFIS version 4.0.57 and higher.
What happens if the report stops working?
This report will be maintained into the foreseeable future. If a software update causes it to stop working, or if we find an error, we'll update the file and let you know there's a new version available, at no additional cost to you.
How long does this report take to run?
The run-time varies depending on how much data is in your database, and how long a date range and how many service providers you select when running the report. However, we have tested the report with large data volumes and it runs quickly and efficiently.
What parameters are included in this report?
Service Provider(s)
Start Date
End Date
Inactivity threshold (for user accounts)
How do I run this report?
Check out our README file.
You may also like...
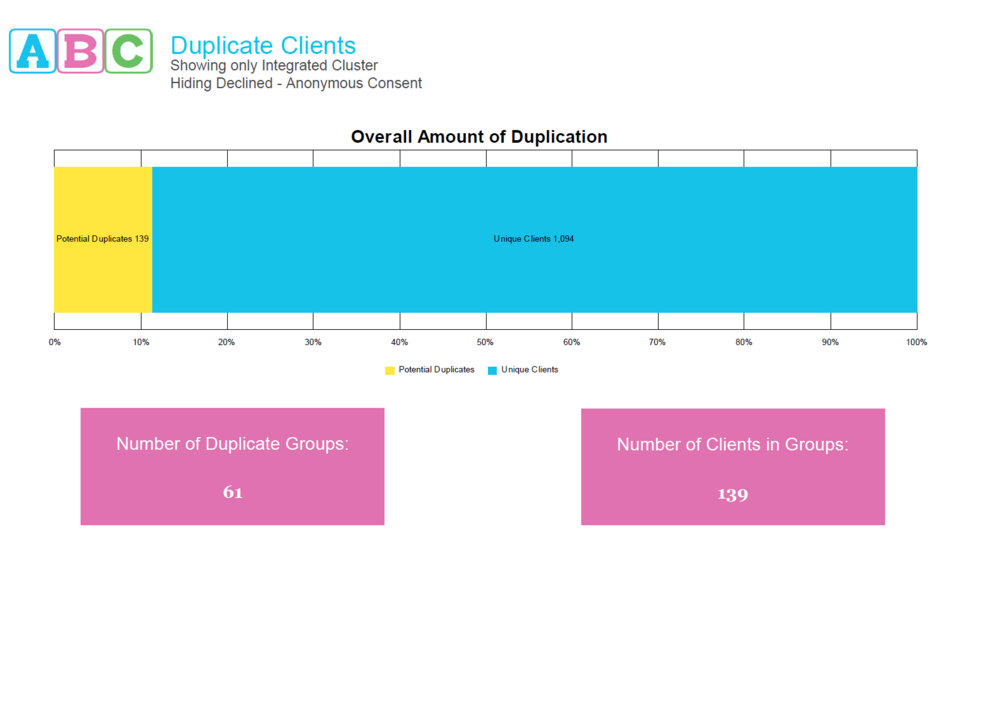
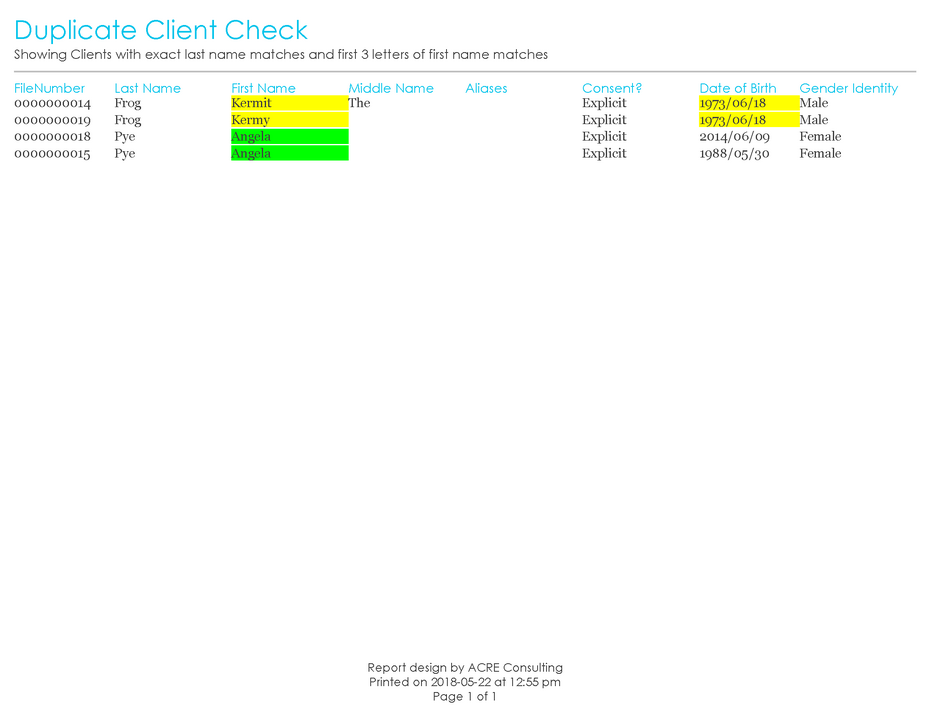
Hunt down those duplicate clients! This report uses advanced methods to identify potential duplicates, helping you identify duplicate clients with misspelled names, swapped middle-first names, and even matching aliases. You get to choose whether to include clients with Declined - Anonymous consent, and whether you want to expand your search to other Clusters. Improve your database's uniqueness today!
Hunt down those duplicate clients! This report uses advanced methods to identify potential duplicates, helping you identify duplicate clients with misspelled names, swapped middle-first names, and eve…

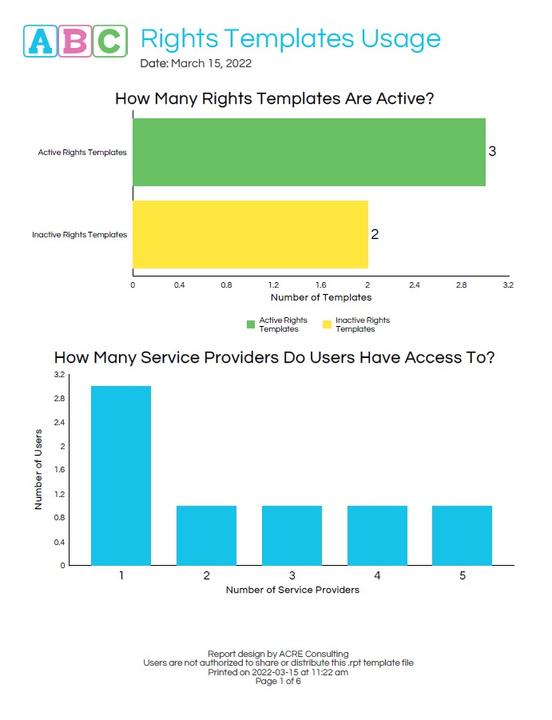
Are staff granted rights that support optimal use of HIFIS?
Do staff have too many rights they don’t use?
Should staff be granted additional rights to support their work?
Hire ACRE Consulting to conduct a Rights Templates Review to answer these questions and more! This service works best if combined with the Client Data Review and the Service Module Review services.
Are staff granted rights that support optimal use of HIFIS?
Do staff have too many rights they don’t use?
Should staff be granted additional rights to support their work?
Hire ACRE Consulting to cond…
Looking for more?